What is Confidential Computing?
During the past decades, the IT industry focused on the protection of data which was stored or “on the fly”. Data encryption and decryption is a commodity service and used by almost all users and companies. Well known examples are VPN for secure connections or BitLocker form Microsoft to encrypt storage devices. But what happens with data during processing? During the step of processing data there is no real security for the data. This is where Confidential Computing becomes necessary.
Why is Confidential Computing important?
In June 2017 the IT world was on alert and IT departments around the world worked overtime due a danger which had the potential to destroy and corrupt infrastructures to their heart. Meltdown and Spectre entered the stage of critical hardware-vulnerabilities. This time the target was the CPU. The heart and brain of PC, Laptop, Server and all other devices using AMD/Intel based processors produced since 1995. These attacks allows a malicious program to access the memory, and other programs and the operating system. This example shows why data encryption and decryption is also important during data processing.
How Confidential Computing works?
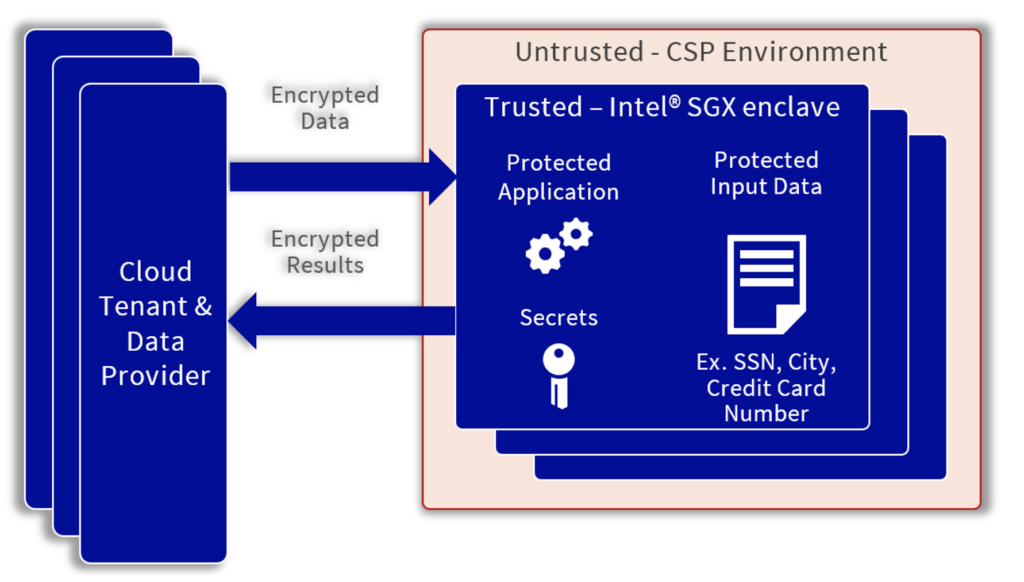
The explanation in the following is based on Intels SGX (Intel® Software Guard Extensions), which is offered by OVHcloud in the server lines with Intel Xeon E-2288G CPU. In addition, OVHcloud offers also AMD Infinity Guard, which is available in AMDs Zen based EPYC processors.
Confidential computing protects data and applications by running them in secure enclaves (see picture below). Enclaves are isolated areas of memory with sensitive application data protected by the CPU (trusted). The code and data in these memory regions are reachable only within the enclave. This isolate the data and code to prevent unauthorized access, even when the compute infrastructure is compromised. Intel® SGX technology represents one of the leading implementations of Confidential Computing. It allows organizations to isolate the software and data from the underlying infrastructure (hardware or OS).
As a result: Users can now run sensitive applications and data on untrusted infrastructure, public clouds, and all other hosted environments. This gives users greater control over the security and privacy of applications and data inside and outside of their established security perimeter.
How can Partner benefit from OVHcloud Confidential Computing offer?
The Confidential Cloud offer provides the following benefits for customers and partners:
- It protects data and application in use
- It helps to secure intellectual property (IP)
- Users can enable encryption across the whole data lifecycle
- Avoids attacks and unauthorized access to data which is processing
- Users have complete control over the data in the cloud
Confidential Computing is important for every user handle sensitive data in their processing. With Confidential Computing the data is save and you can separate sensitive data from more common data during operations. E.g., using sensitive data to train an ML model.
With Confidential Computing, Partners can offer a range of products and solutions for customers with a need for secure environments. This could be solutions for financial services or other areas where personal data is processed.
OVHcloud: Offering and Case Study
For more information about our Confidential Computing portfolio visit: https://www.ovhcloud.com/en/bare-metal/uc-confidential-computing/
Please visit https://www.ovhcloud.com/en/case-studies/securitee/ to find out how our partner SECURITEE take advantage of the OVHcloud portfolio to provide a Confidential Computing solution.
Our collaboration with OVHcloud has been smooth and efficient. Our joint product offering is arguably the most secure and readily available cloud computing solution – a real first in the European market.
Tristan Jose, COO of SECURITEE
