[15 min read]
This article is primarily intended for an international audience of networks professionals, information security specialists, security researchers and technical stakeholders. Whether or not you belong to the target audience, but particularly if you do not, please be mindful of your conclusions.
Table of Contents
- 1. Introduction
- 2. Carpet-bombing is more popular than ever
- 3. The rise of packet rate attacks: billion(s) of packets per second
- 4. Ever-growing hyper-volumetric attacks: 4 Tbps reached
- 5. Institutional and residential ISPs spoofing
- 6. Operation PowerOFF and consequences
- 7. Conclusion and closing words
1. Introduction
Welcome to this brief retrospective about the DDoS attack landscape in 2024, as seen from OVHcloud’s vantage point.
Like any other cloud provider, we deal with DDoS attacks on a daily basis, automatically detecting and mitigating hundreds of attacks each and every day. We operate our own worldwide anti-DDoS infrastructure, built from systems designed and developped internally. To date, we have more than 50 Tbps of total mitigation capacity, located at the edge of our network as well as in dedicated scrubbing centers, for which we keep adding more capacity each year to keep up the pace.
Thanks to our global backbone and numerous points of presence, we do have a sensible view of Internet traffic and trends, especially when speaking about network-layer DDoS attacks. That’s why we wanted to expose and discuss several topics we encountered during the year, in the hope you may learn something or find it useful for your own sake.
Context aside, let’s dive into this retrospective: what a year! 2024 was definitely an important turning point in DDoS history, at least from our point of view. From good’ol DDoS techniques coming back at scale, to several record-breaking attacks, we’ve seen quite a lot, and no one doubts that 2024 events will be the main driving factor for anti-DDoS infrastructure planning in the coming years.
2. Carpet-bombing is more popular than ever
During the year 2024, we observed a sudden increase of attacks leveraging a technique known as “carpet-bombing”. This attack technique is named after a brutal warfare method which consists in methodically bombing every bit of surface of a large area. Similarly, “carpet-bombing” in our context refers to attacks targeting many more IP addresses than those servicing the actual target.
Carpet-bomb attacks are used in an attempt to evade anti-DDoS systems. This is because they are much harder to detect and mitigate automatically: by sending a few hundreds megabits per second per IP, attacker can reach huge volumes while evading (at least partially) detection heuristics and possible mitigation actions. Simply put, instead of trying hard to bomb a target, just bomb the whole area around it.
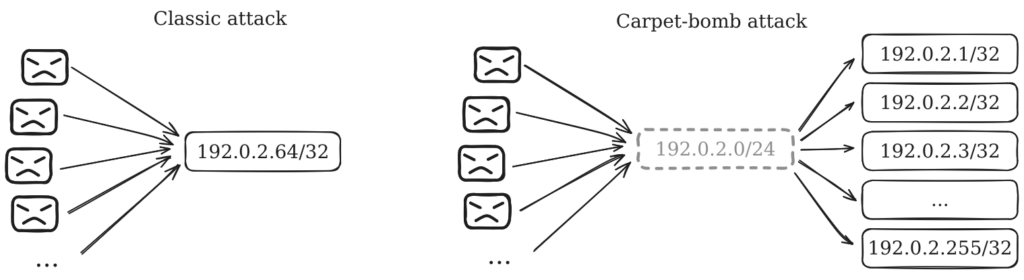
By targeting a large number of closely-related IPs (e.g., belonging to a larger prefix), attackers rely on common design characteristics of many networking infrastructures: you generally want to assign an address range to a physical or logical part of your infrastructure for several reasons. Briefly, this is often required because of technical limitations on networking devices and appliances, as well as what is humanly possible to understand and manage: whether for hardware or humans, you cannot store millions to billions entries in routing table, access control lists, etc. At some point, you must aggregate your resources.
Back to the main topic, carpet-bomb attacks are a double-edged sword: the part of the attack possibly reaching your final target will probably not be powerful enough to take it down, but you take a better chance at evading defenses. This is because it’s much more difficult to identify with confidence what is legitimate from what is not, but also to scrub traffic without impacting legitimate users. In the end, the total attack traffic leaking defenses may impact a significant chunk of the hosting infrastructure, even if traffic to any single destination IP would not have been enough to take it down.
2024 has been a turning point in carpet-bomb trends from our point of view. Attackers started to leverage this technique more and more often, with mixed results, and led us to rethink how to deal with such attacks. For some times now, we are testing and calibrating our solution to the issue, but need to treat carefully: facing such a radical threat may lead to actions which could be impactful for other customers. There’s a difficult balance between sensitivity (i.e., make sure you don’t detect or mitigate too much) versus specificity (i.e., make sure you don’t miss anything notable). We will keep working hard to address the matter and minimize disruption.
3. The rise of packet rate attacks: billion(s) of packets per second
In June 2024, we published a blog article titled “The Rise of Packet Rate Attacks: When Core Routers Turn Evil”.1 This article was presenting our findings related to small core routers participating in DDoS attacks, and was a byproduct of our investigations about a concerning trend with packet rate attacks. Readers should refer to the cited article to have a detailed explanation of how they work, and why these attacks remain a longstanding threat.
Since the end of 2023 and beginning of 2024, we noticed a large increase of packet rate attacks both in frequency and intensity, with intensity reaching an all-time high at the end of summer.
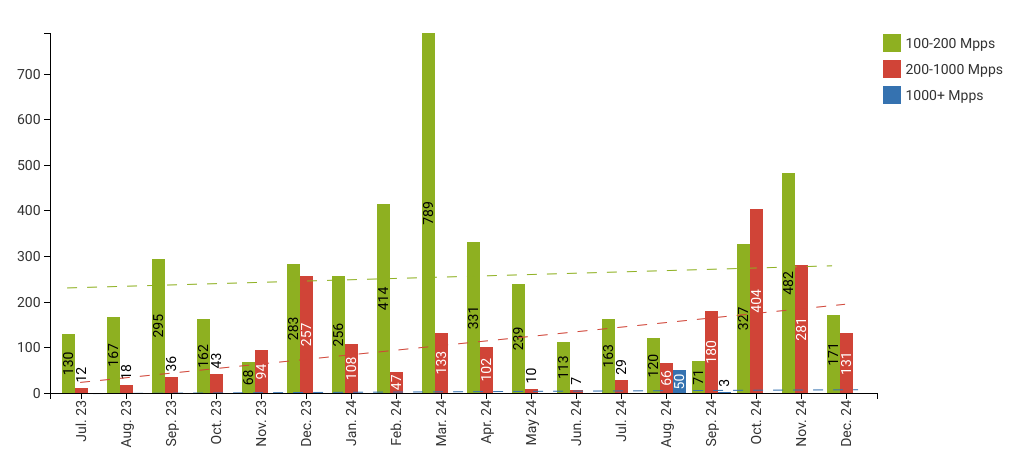
During August, we dealt with more than 50 packet-rate attacks rating over one billion packets per second. Note that the highest publicly known packet rate attack at this time was the 840 Mpps attack we mitigated in April of the same year.
However, this attack campaign not only reached the billion packets per second milestone, but actually went much higher with packet rates up to 1.9 billions packets per second. Such a rate was mind-blowing for our teams, and rightly so! A symbolic threshold was not only reached, but largely exceeded. Since then, several organizations reported observing 1+ Gpps attacks and more: for instance, Cloudflare reported rates greater than 2 billions packets per second 2 in an attack campaign which occurred just a few days after the attack campaign targeting OVHcloud and its customers, while Global Secure Layer reported a single 3.15 billions packets per second attack at the same time.3
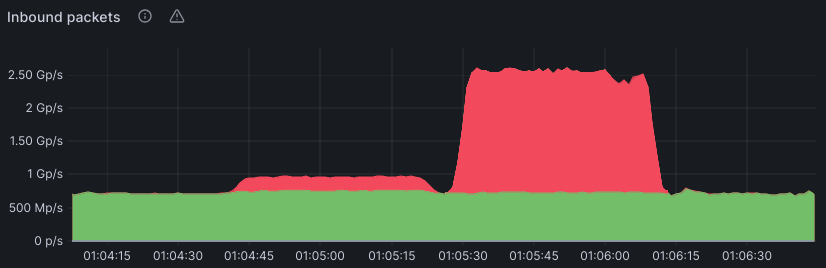
Before moving on to the next topic, a notable fact related to this attack campaign is that it was heavily leveraging carpet-bombing techniques targeting up to thousands of IPs over hundreds of customers. Attackers are definitely not scared about trying to impact a lot of people in an attempt to take down a specific service, despite the increased attention this kind of attack generates.
4. Ever-growing hyper-volumetric attacks: 4 Tbps reached
During the month of September, we were thrilled to mitigate our very first 3+ Tbps attack ever. However, it was just a warning shot for what was to come: another massive attack campaign during October. Although we had only seen a handful of 2+ Tbps attacks in OVHcloud history, this two weeks campaign led to more than 40 attacks ranging from 2 Tbps up to a record-breaking (at the time) 4.2 Tbps attack.
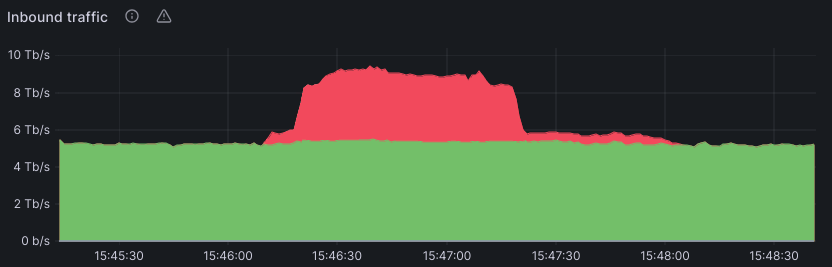
Since most attacks exhibited similar characteristics, we will focus on the biggest one. At the time it happened, this attack was the largest bit rate attack ever (compared to previous publicly known records). It leveraged multiple attack vectors at once : TCP ACK flood accounted for ~60% of the total traffic, direct-path UDP flood accounted for 20%, while the remaining 20% was performed with various UDP reflections (mostly DNS).
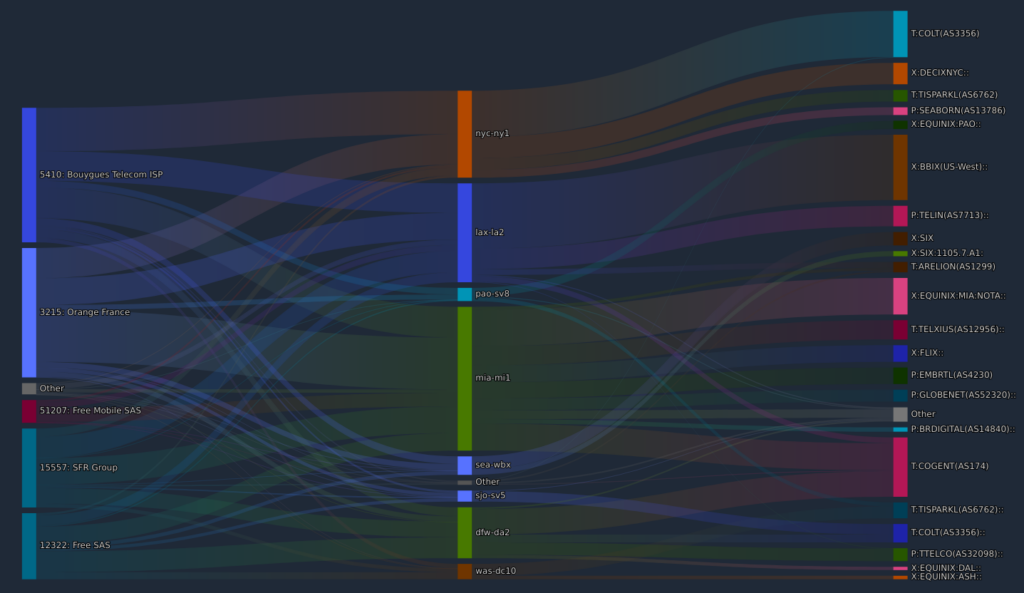
We identified approximately 150,000 source IPs, mostly owned by residential ISPs from Europe and North America. For the most part, attackers did not seem to leverage source spoofing, since our data shows that traffic from IPs belonging to an ISP came from direct peering with said ISP or a related exchange/transit provider. However, the surprising amount of unique source IPs and the significant volume going through exchange/transit suggest there is possibly some undetected spoofing. Total count of unique source IPs should thus be considered with a lot of salt.
One notable thing also is that few tens of attacking IPs were sending 1+ Gbps each, which suggests high-grade residential connections with lot of upload bandwidth. Moreover, according to our analysis, all the direct-path attack traffic (approximately 80% of total) was originating from a Mirai-based botnet.
All these findings are in-line with conclusions from various cloud providers and analysts, showing the continuously growing threat of compromised IoT devices and home routers. 8 years after the initial release of Mirai code, this botnet family is still actively used to attempt disrupting the online economy.
Readers should note that since the 4.2 Tbps attack we just discussed, several actors reported even higher rates such as the 5.6 Tbps at Cloudflare in late 2024 4, or the more recent 6.5 Tbps attack reported by Nokia in February 2025.5
5. Institutional and residential ISPs spoofing
Last but not least, we also observed another growing trend during the year: the large-scale spoofing of major residential ISPs.
We are used seeing many IPs belonging to residential ISPs participating in attacks, as a lot of compromised devices are located within those networks (“I see you.. Internet of Things!“). However we observed a growing number of attacks using those IPs, but originating from far abroad: for instance, we found traffic using IPs of major French ISPs (Orange, SFR, Bouygues, Free) but originating from the US west coast or Asia-Pacific, and coming through unrelated peering partners (despite us directly peering with said ISPs!). In this situation, source IPs are obviously spoofed.
We also observed the same technique being used by spoofing large institutional actors, such as state actors or government-backed organizations which own several Internet prefixes.
An explanation about these attacks is that attackers are trying to leverage hypothetical bypasses in defense layers such as lax rate control, allow/forward rules, and others. This makes sense because, as a major european actor based in France (with a significant business in France), we could have considered being less strict with French IPs. It’s also much harder to react against an attack that could lead to actions shutting down legitimate traffic as well, which will be the case if one decides to deny entire ranges against such attacks (we don’t do that!).
Moreover, we sometimes have customers asking us to disable any DDoS protections for their IPs, because “we can trust them”. But that’s not how the Internet works. As a provider, protecting yourself against external spoofing is maybe doable on paper, but in reality, it’s close to impossible. That’s why we have security measures, and bypassing them even with the best intent will often prove itself as a bad decision, not only for the requesting customers but also for any other services which could be impacted because of this.
Finally, this issue highlights a crucial need for DDoS attacks remediation: all network operators have a part to play in preventing IP spoofing. This shall be done at two levels: at server/switch level by locally preventing IP spoofing from a specific host, and at the network level by preventing outbound traffic with source IPs not owned by the network operator.
6. Operation PowerOFF and consequences
Operation PowerOFF is an ongoing joint operation by several law enforcement agencies around the world, specifically aimed at shutting down DDoS-for-hire operations. At the beginning of November 2024, they closed the infamous dstatc.cc platform, which provided means for attackers to benchmark the capabilities and effectiveness of DDoS attacks. Along with this closure, multiple DDoS-for-hire websites were closed, botnets dismantled, and cybercriminals arrested.6
This event led to a huge decline in frequency and intensity of network-layer DDoS attacks targeting OVHcloud infrastructures and customers. For some time, our attack statistics were quite below their usual levels of the past two years. This fact proves the effectiveness of global coordinated actions to take down botnets, and should call for more.
7. Conclusion and closing words
In the past, network-layer DDoS attacks were often dismissed as a minor inconvenience, or even a solved problem. However, as year 2024 proved, they still represent a growing and longstanding threat which must be addressed seriously. That’s one reason why DDoS attacks are often stated in threat reports emanating from various actors, such as a recent threat report published by the French national information security agency (ANSSI) in February 2025.7
Although application-layer attacks (especially HTTPS) are more popular nowadays for several reasons, no one should dismiss network-layer attacks as an unsignificant risk. If dealing successfully with billions of packets per second or several terabits of traffic may seem like an achievement for a few of us, it is a very difficult challenge for many. Be prepared!
Fighting against these threats must be done at both an individual and a global level. Coordinated efforts are a necessity in today’s DDoS landscape and will probably be even more important in years to come. It may sound scary, but remember it actually has a positive impact as demonstrated once again by Operation PowerOFF.
Thanks for reading.
- https://blog.ovhcloud.com/the-rise-of-packet-rate-attacks-when-core-routers-turn-evil/ ↩︎
- https://blog.cloudflare.com/ddos-threat-report-for-2024-q3/ ↩︎
- https://globalsecurelayer.com/blog/unprecedented-3-15-billion-packet-rate-ddos-attack ↩︎
- https://blog.cloudflare.com/ddos-threat-report-for-2024-q4/ ↩︎
- https://arstechnica.com/security/2025/03/massive-botnet-that-appeared-overnight-is-delivering-record-size-ddoses/ ↩︎
- https://www.europol.europa.eu/media-press/newsroom/news/law-enforcement-shuts-down-27-ddos-booters-ahead-of-annual-christmas-attacks ↩︎
- https://www.cert.ssi.gouv.fr/cti/CERTFR-2025-CTI-001/ ↩︎
Christophe Bacara
Technical Lead - Network Security Engineering at OVHcloud
